Uber Eats GPS Spoofing Deactivation Risk: Evidence and Prevention
A 2026 guide to Uber Eats location warnings, GPS spoofing account risk, iPhone evidence collection, and QPin system-location testing.
Uber Eats GPS Spoofing Deactivation Risk: Evidence and Prevention
Searches around Uber Eats account deactivation for GPS spoofing are usually fear-driven. A courier sees a location warning, a false-location message, a pin mismatch, or a GPS drift pattern and worries that the account may be reviewed. The useful response is to separate evidence, risk, and system-level iPhone location testing.
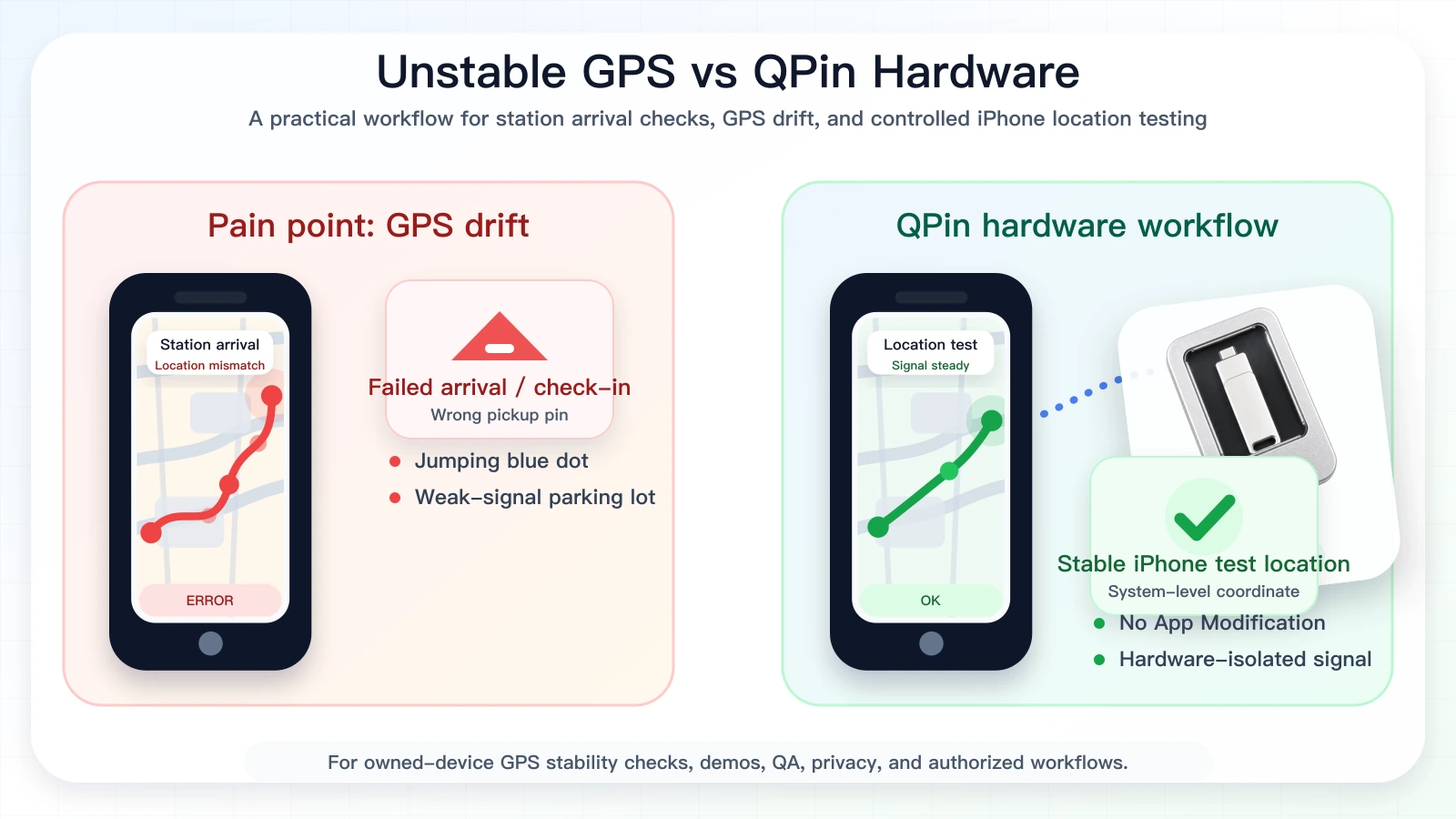
QPin cannot control Uber Eats account decisions. QPin can modify iPhone system location in supported workflows, keep the Uber Eats app untouched, and help users document GPS behavior on owned devices. That makes it useful for support evidence, QA, privacy workflows, demos, and authorized troubleshooting.

Watch the QPin Uber Driver GPS Demo
This short video shows QPin changing the iPhone system GPS location through an external hardware workflow. Uber Driver then reads the updated iOS location on the same device. Use it as a visual reference for system-level location behavior; each app can still apply its own account, network, sensor, and policy checks.
QPin iPhone GPS Modifier Demo: Uber Driver Reads Updated iOS Location
Why Location Warnings Happen
A location warning can come from intentional misuse, but it can also come from ordinary technical problems:
- GPS drift in dense urban streets;
- pickup pins placed at the wrong entrance;
- stale Wi-Fi or cellular positioning;
- VPN or network mismatch;
- delayed app refresh;
- route timing that does not match the iPhone location stream;
- weak signal inside restaurants, malls, or apartment complexes.
For serious risk management, do not guess. Build a record.
Separate Misuse Risk From False-Positive Risk
The phrase "GPS spoofing deactivation risk" combines two different situations. One is actual deceptive location behavior, which can violate platform rules. The other is a false-positive-looking situation where a rider is physically present but the phone, map pin, or app state looks inconsistent. A useful Uber Eats article must handle both without promising account outcomes.
QPin belongs in the evidence and testing side of that discussion. It can set a known iPhone system coordinate, keep Uber Eats unmodified, and help users show whether Apple Maps, Uber Eats, and a selected coordinate agree. That evidence does not override Uber Eats decisions, but it makes a support or QA conversation much more concrete.
Evidence Chain for Location Mismatches
If Uber Eats, Apple Maps, and the physical location disagree, collect:
QPin can help when you need to reproduce a known coordinate. Set a controlled iPhone system location, verify it in Apple Maps, then compare Uber Eats. If Apple Maps and Uber Eats disagree, the issue is probably not simple raw GPS.
Prevention Without False Promises
Prevention should mean reducing avoidable location anomalies, not promising account outcomes:
- Keep Uber Eats original and unmodified.
- Do not use cloned or patched courier apps.
- Keep Precise Location enabled.
- Keep Wi-Fi on for iOS positioning support.
- Avoid VPN during live app workflows unless required and allowed.
- Check Apple Maps before contacting support.
- Use QPin only for owned-device testing and authorized workflows.
- Return to real GPS after testing.
This positions QPin as a location stabilizer and evidence tool. It is not a legal service or an account-decision tool.
Compliance Note
QPin is not affiliated with Uber Eats, Uber, DoorDash, Amazon Flex, Spark Driver, Walmart, Lyft, or any delivery platform. Users should follow the rules of the apps and platforms they use.
QPin is designed for owned-device testing, GPS stability checks, demos, privacy, QA, support reproduction, and authorized workflows. Platform decisions remain controlled by the platform.
Related Guides
- Uber Eats false location detected guide
- iOS location spoofing for Uber Eats drivers
- Uber Eats iPhone GPS drift
- Fix Uber Eats map inaccuracy for UK riders
FAQ
Can GPS spoofing lead to Uber Eats account review?
Platform rules can treat deceptive location behavior as a serious issue. This article focuses on evidence collection, GPS drift diagnosis, and authorized testing, not on evading platform review.
Can QPin prevent deactivation?
No. QPin cannot control Uber Eats account decisions. It can help test and document iPhone system-location behavior in supported workflows.
What evidence should I collect for a location mismatch?
Collect Apple Maps screenshots, Uber Eats screenshots, address, time, app version, iOS version, network state, VPN state, and any repeated GPS drift pattern.
